A recent piece of investigative journalism by The Bangkok Post has provided evidence of Thailand acquiring an advanced electronic surveillance capability. Traditionally a non-NATO treaty ally of the United States, Thailand has provided high-level intelligence to the United States, as the Wikileaks Cablegate Thailand cables made clear. In exchange, Thailand was likely able to rely on obtaining intelligence from the ‘Five Eyes’ intelligence-gathering network consisting of the United States, the United Kingdom, Australia, New Zealand, and Canada, especially regarding areas of shared concern, for example, the situation in the Deep South or high-value targets.
However, the breakdown of relations with the United States around the end of last year, culminating in the statements made by US Assistant Secretary of State Daniel Russel in January 2015, clearly posed a dilemma for Thailand: how to obtain a reliable surveillance state capability equivalent to that of a more advanced country. Thailand would have faced only two choices.
The first was to source a cooperative solution from a major power such as Russia, home to Kaspersky Labs, which is rumored to possess close links to the KGB, or from the People’s Republic of China. However, Thailand is not a traditional ally of either, and the prospect of introducing advanced Russian or Chinese e-warfare capabilities into Thai security apparatus facilities may have posed a greater threat than the advantages. This possibility of a compromised intelligence network including command and control facilities may also be a reason for the delay in purchasing the three Chinese submarines.
The second option would have been to source an advanced electronic surveillance suite from off-the-shelf vendors operating in a murky legal environment where such software can be classified as ‘military equipment’. Like many other countries developing towards an advanced police state, including the usual suspects Azerbaijan, Kazakhstan, and Uzbekistan, Thailand apparently chose this option, becoming by December 2014 the customer of the now notorious Hacking Team, a Milan-based information technology developer of intrusion and surveillance capabilities. This development was practically announced in February 2015, when the Thai military advertised the recruitment of officers to join a new ‘Cyber Warfare’ unit under the Directorate of Joint Operations of the Royal Thai Armed forces.
Hacking Team’s main product is the Remote Control System ‘Galileo’. However, the Hacking Team was itself hacked on July 5, 2015, revealing all its internal emails and source code, which The Bangkok Post has partially analysed from the Wikileaks site.

Figure 1: Part of (the Heavily Compromised) Hacking Team’s Presentation
The Wikileaks Hacking Team data for Thailand shows Hacking Team’s software suite was acquired by the Royal Thai Army and the Corrections Department of the Royal Thai Police in cooperation with Israel-based Nice Systems and partner Thai firms Placing Value, Netsurplus and Samart Comtech.
The suite includes all the capabilities you might expect from an advanced intelligence agency. These include the ability to covertly collect emails, text messages, and phone call histories; perform keystroke logging; uncover search history data and take screenshots; record audio from phone calls; use phones to collect noise and conversations by remotely switching on the telephone; activate the telephone’s camera; and hijack telephones GPS systems. The Remote Control Software (RCS) was capable of utilizing a number of known and ‘Zero-Day’ (unknown to anti-virus companies and previously unused) hacking exploits against software including Adobe Flash.
Companies such as Hacking Team have been heavily criticized for selling hacking software to repressive governments, such as Sudan, Bahrain, and Saudi Arabia. In particular, Hacking Team sold software to Sudan in 2012, which led it to being investigated by the United Nations Panel on Experts for the Sudan for infringing a UN prohibition on selling “‘military … equipment’ or ‘assistance’ related to prohibited items” according to UN Security Council resolutions 1556 (2004) and 1591 (2005). Hacking Team’s response was to evade questions.
The RCS has been detected by counter-intrusion experts on the software of activists and journalists, perhaps one of the purposes behind its purchase by the Royal Thai Army Military Intelligence Command.
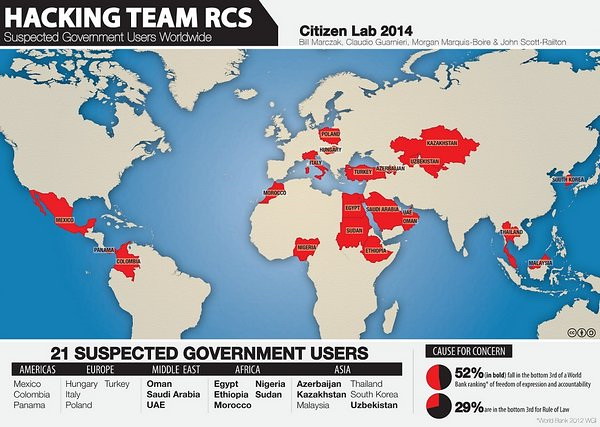
Figure 2: Suspected Government Users of Hacking Team Software
The development of military-grade e-warfare/surveillance state capabilities in a free and democratic country can be justified only if there exists a regulatory framework. For example, Malaysia is also apparently a client of Hacking Team, as is South Korea, but both have civilian governments and regulatory frameworks regarding national security. However, Thailand possesses a weak framework, as The Bangkok Post makes clear in quotes sourced from the leaked Hacking Team emails: Thailand is “characterised by poor legislation and no LEA [law enforcement agency] or intelligence connectivity to telecom service providers".
This means that there is a legal vacuum and the Royal Thai Army at present does not have the capability to directly interface with approximately 10 internet gateways provided by telecommunications operators in the same way as the US did via the NSA Warrantless Surveillance Program (2001-2007) and successor programs, which Congress has recently begun to roll back. However, according to The Bangkok Post, Thailand’s military government is introducing legislation, the proposed Cyber Security Bill, designed to permit much broader warrantless application of electronic surveillance (under Section 35). And, one stated goal of the military government is a single gateway to the internet based in Bangkok, which would facilitate the development of the surveillance state.
The Bangkok Post notes that National Human Rights Commissioner Dr. Niran Pitakwatcharahas has come out against the use of electronic intelligence and e-warfare against Thai citizens: "It is a violation of democratic principles, in which the state does not have the right to threaten the privacy of individuals… Thailand needs to be aware that it is at risk of violating the right to privacy and freedom of expression, under the disguise of 'national security' concerns…” Crucially, Dr. Niran argues that there is a need to differentiate between the needs of the state and the needs of the government. However, under Thailand’s military governments there has traditionally been no distinction between the two.
It has been noted that unrestricted electronic mass surveillance creates a ‘Culture of Fear’ among the citizenry in countries which have implemented advanced electronic intelligence and surveillance operations in an arbitrary and unchecked manner. Unfortunately, at present Thailand under Section 44 (a ‘Rule by Diktat’ provision in the present Interim Charter) does operate in such an atmosphere. Electronic mass surveillance can target both schoolchildren and adults, as detailed in the US 2014 Human Rights Report on Thailand and discussed here.
Also, the advanced e-warfare options offered by software such as the RCS offer the capability to spy on any citizen at any time without the citizen even being aware – a development of the advanced police state known as ‘panopticism’ and described in the novel 1984. It should be noted that 1984 cannot be read in public in Thailand. And, now, perhaps, we know another reason why.
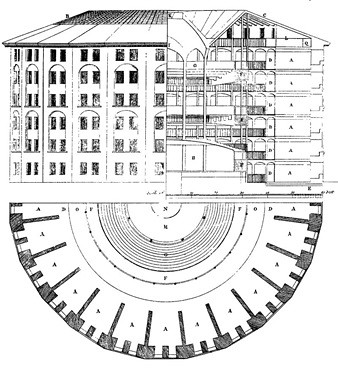
Figure 3: The ‘1984’ Panopticon Effect – Users of Smart Phones Are Similar to Prisoners
Prachatai English is an independent, non-profit news outlet committed to covering underreported issues in Thailand, especially about democratization and human rights, despite pressure from the authorities. Your support will ensure that we stay a professional media source and be able to meet the challenges and deliver in-depth reporting.
• Simple steps to support Prachatai English
1. Bank transfer to account “โครงการหนังสือพิมพ์อินเทอร์เน็ต ประชาไท” or “Prachatai Online Newspaper” 091-0-21689-4, Krungthai Bank
2. Or, Transfer money via Paypal, to e-mail address: [email protected], please leave a comment on the transaction as “For Prachatai English”
